Coin Metrics State of the Network is an unbiased, weekly view of the crypto market informed by our own network (on-chain) and market data.
Key Takeaways
- Quantum computers do not currently pose a challenge to blockchain cryptography, but recent progress has compressed timelines and moved the industry towards active preparation.
- Roughly 6.9M BTC is estimated to be quantum exposed due to legacy address types and key reuse, with ~1.7M BTC (9% of supply) sitting dormant in Satoshi-era coins that cannot easily migrate.
- Quantum risk varies across blockchains due to address structures, signature schemes, and consensus models, with ecosystems progressing on proposals and post-quantum roadmaps to adopt new signature schemes.
Introduction
Rapid progress in quantum computing is turning a once-distant possibility into a concrete challenge for the cryptography that underpins blockchains. Recent research from Google’s Quantum AI group found that the resources and timeline required for a quantum computer capable enough of breaking the elliptic-curve cryptography securing Bitcoin and other blockchains, is compressing. Coinbase’s quantum advisory board has also voiced that while no such machine exists today, the time to begin migrating to post‑quantum cryptography is now.
As this risk moves closer to reality, developers, network participants, investors and large institutional holders have an important role to play in steering decentralized ecosystems towards a post quantum future.
In this issue of State of the Network, we break down quantum computing's risks to blockchain cryptography, focusing on Bitcoin’s exposure, the debate over dormant coins and how Ethereum and Solana are approaching post-quantum readiness.
Understanding The Quantum Risk Ahead
Blockchain security depends on cryptographic signatures that are hard for classical computers to break but potentially vulnerable to quantum computers. Today, Bitcoin, Ethereum, and most other networks use elliptic‑curve signatures (such as ECDSA and BLS) to prove that the holder of a private key authorized a transaction. Quantum algorithms such as Shor’s can, in principle, derive private keys from their corresponding public keys, turning any address with an exposed public key into a potential target once such a machine exists.
This threat takes two main forms, depending on whether public keys are already exposed or revealed during a transaction:
- At‑rest (long‑range) attacks: Targets wallets, validator keys, and contracts whose public keys are already visible onchain, where a future quantum computer could derive private keys and steal funds without any new action by the owner.
- In‑flight (short‑range) attacks: Target transactions in the brief window between when a public key is revealed in a spend and when the transaction is finalized, where a fast quantum computer could race the network to sign a conflicting transaction. Bitcoin’s ~10-minute block time creates a larger vulnerability window than faster chains like Ethereum (~12 seconds) or Solana (sub-second finality).
Bitcoin’s Quantum Exposure
Bitcoin’s quantum exposure is primarily at the wallet level and a function of how its UTXO model and address types handle public keys. Each unspent transaction output (UTXO) is locked to a script that ties back to a public–private key pair. As long as the public key stays hidden, it is hard for a quantum attacker to target. But once that key is onchain, a future quantum computer could derive the private key and forge a valid spend.
The risk to Bitcoin therefore stems from whether a public key has been exposed, and varies by address type and re‑use.
- P2PK (pay‑to‑public‑key): Includes some of the earliest coins from the “Satoshi era,” early miners and Satoshi’s coins themselves. These are the most vulnerable because the public key is explicitly visible on the ledger, making them long‑range targets.
- Re-used P2PKH (legacy pay‑to‑public‑key‑hash): Addresses where the public key is hidden at first but is revealed when the address spends, leaving any remaining balance in a reused address more exposed.
- Re-used P2SH (pay‑to‑script‑hash): Addresses that hide a script until spent but often lock funds with the same keys for a long time, so once they are used and reused, several public keys can end up exposed.
- P2WPKH / P2WSH (SegWit): Native SegWit outputs that keep public keys behind a hash until spend and are typically used with fresh, non‑reused addresses, making them relatively lower risk outside the brief spend window.
- P2TR (Taproot): Addresses that improve flexibility and privacy but embed a tweaked public key directly in the address, giving a future quantum attacker a visible key to target from the start.
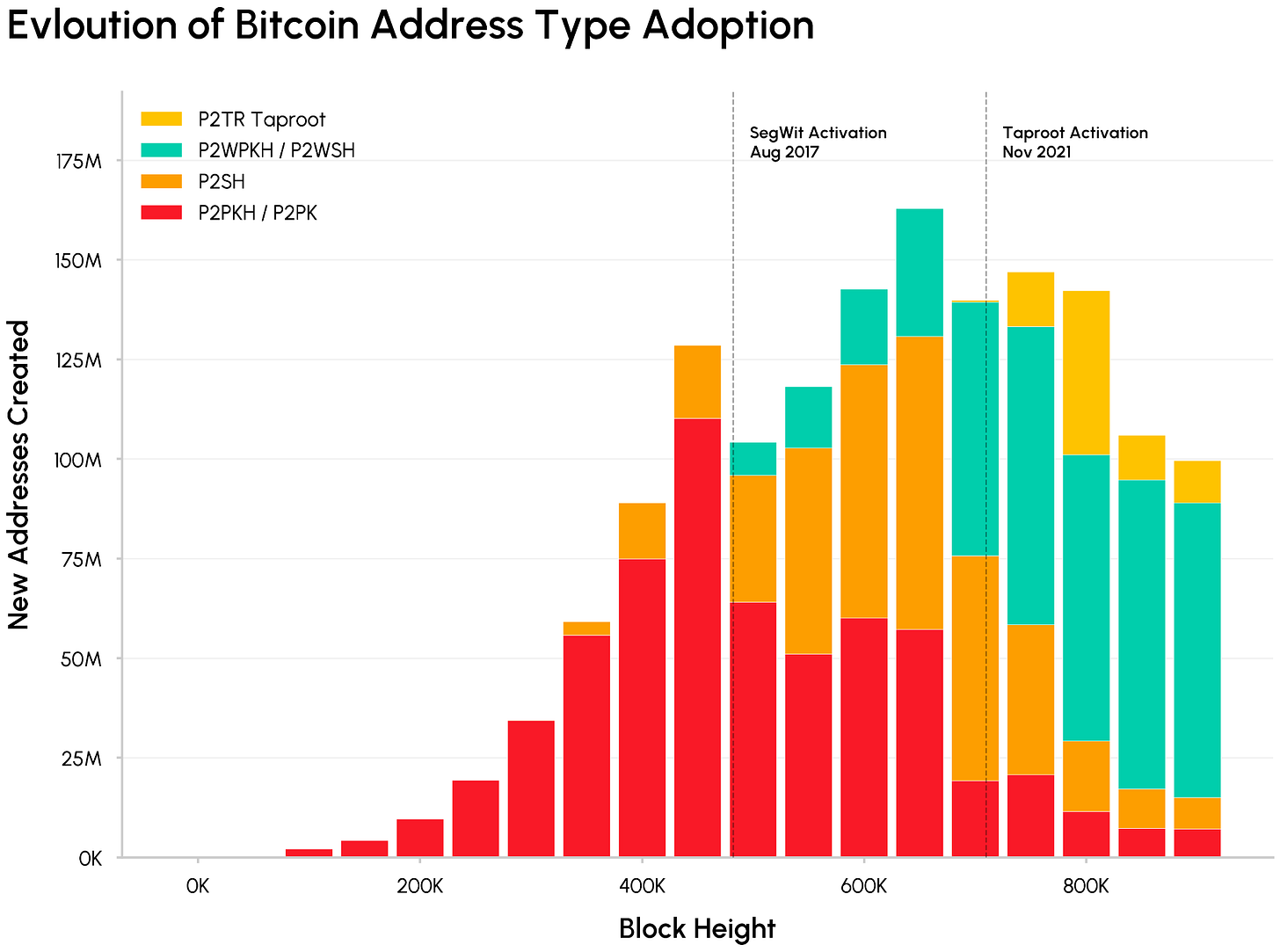
The chart below shows how adoption of these address types has evolved over Bitcoin’s history, highlighting the shift from legacy P2PK/P2PKH toward SegWit outputs. This is gradually moving new coins into addresses that are structurally less exposed to quantum attacks.
How much Bitcoin is vulnerable?
According to estimates from Project Eleven and Google’s March quantum whitepaper, about 6.9M BTC sit in addresses where public keys are exposed, either through legacy P2PK outputs where the key was visible from day one, or through address reuse where spending broadcast it permanently.
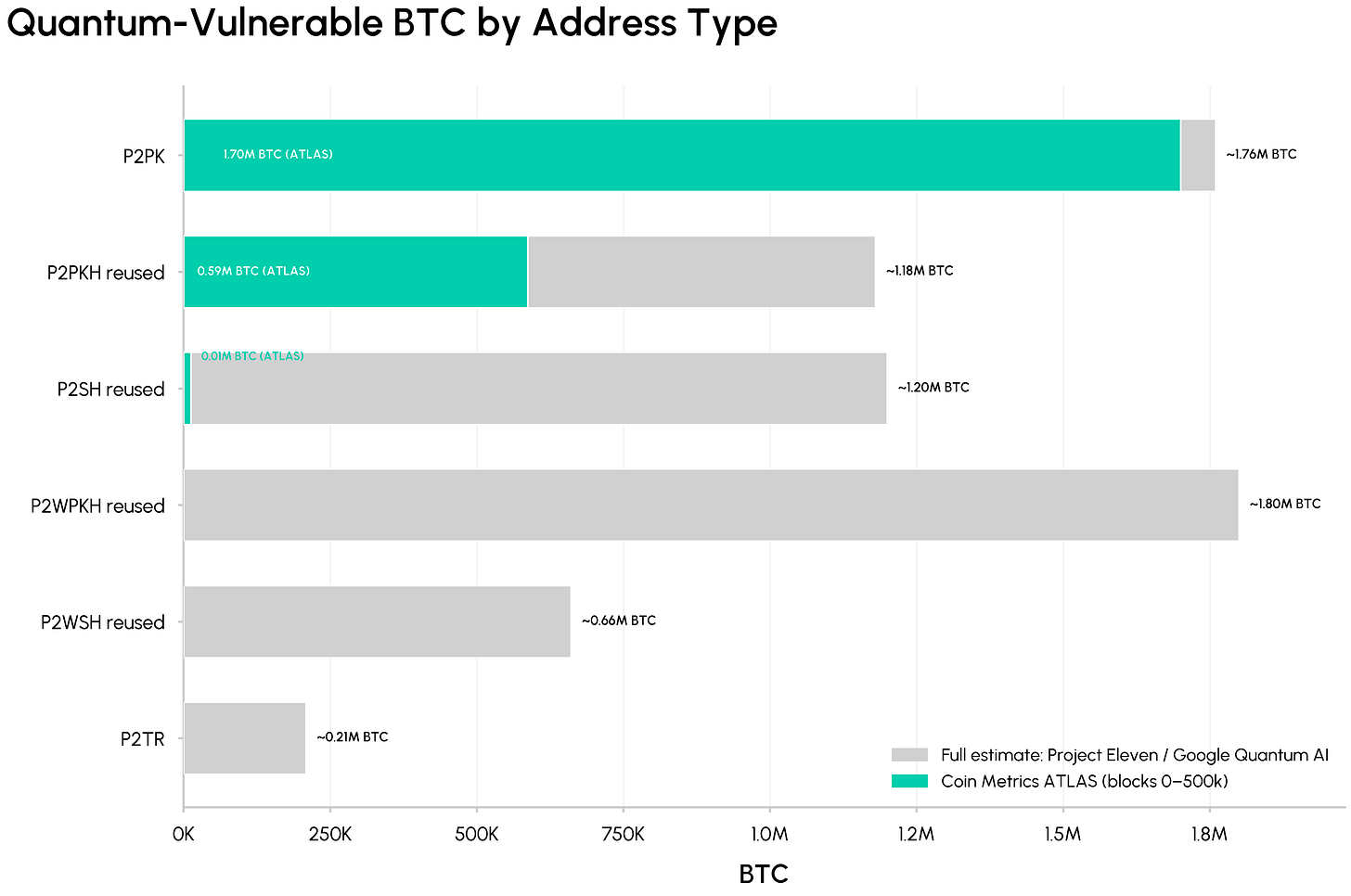
Source: Coin Metrics ATLAS & Project Eleven
Using Coin Metrics ATLAS we scanned Bitcoin's first 500,000 blocks and confirmed ~2.3M BTC in vulnerable addresses, ~1.7M of which are likely P2PK coinbase outputs from the Satoshi and early miner era. The remaining ~4.6M vulnerable BTC sits predominantly in blocks created after 2017. As seen in the address type adoption, legacy P2PKH creation never fully stopped, and reuse across newer formats grew in the years since SegWit and Taproot launched.
The Dormant Coin Dilemma
A central flashpoint of the quantum debate is the fate of Bitcoin’s dormant coins and Satoshi’s coins. Roughly 1.7M BTC (~9% of supply) has never moved since the early years and sits in legacy address types whose public keys are exposed or would be revealed the moment they spend. This pool includes an estimated ~1.1M BTC linked to Satoshi Nakamoto, spread across ~22,000 accounts with roughly 50 BTC rather than a single wallet.
These “Satoshi-era” coins present a unique challenge. Deciding if or how to protect them has become one of Bitcoin’s most contentious coordination problems, since that portion of supply cannot voluntarily participate in the migration. Proposed community responses range from maintaining the status quo (not touching them) to interventions like freezing, burning, or rate-limiting spending.
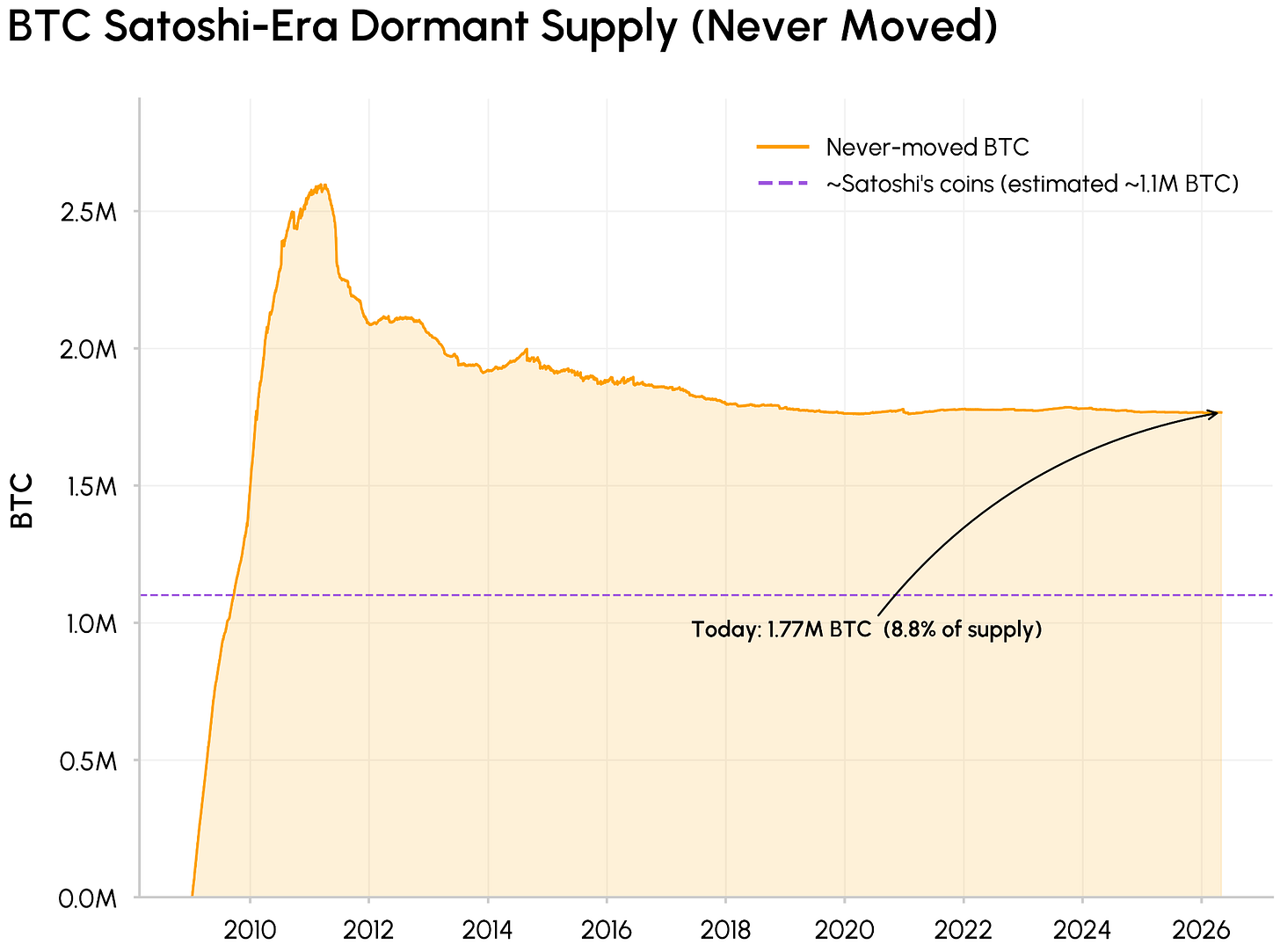
Source: Coin Metrics Network Data Pro
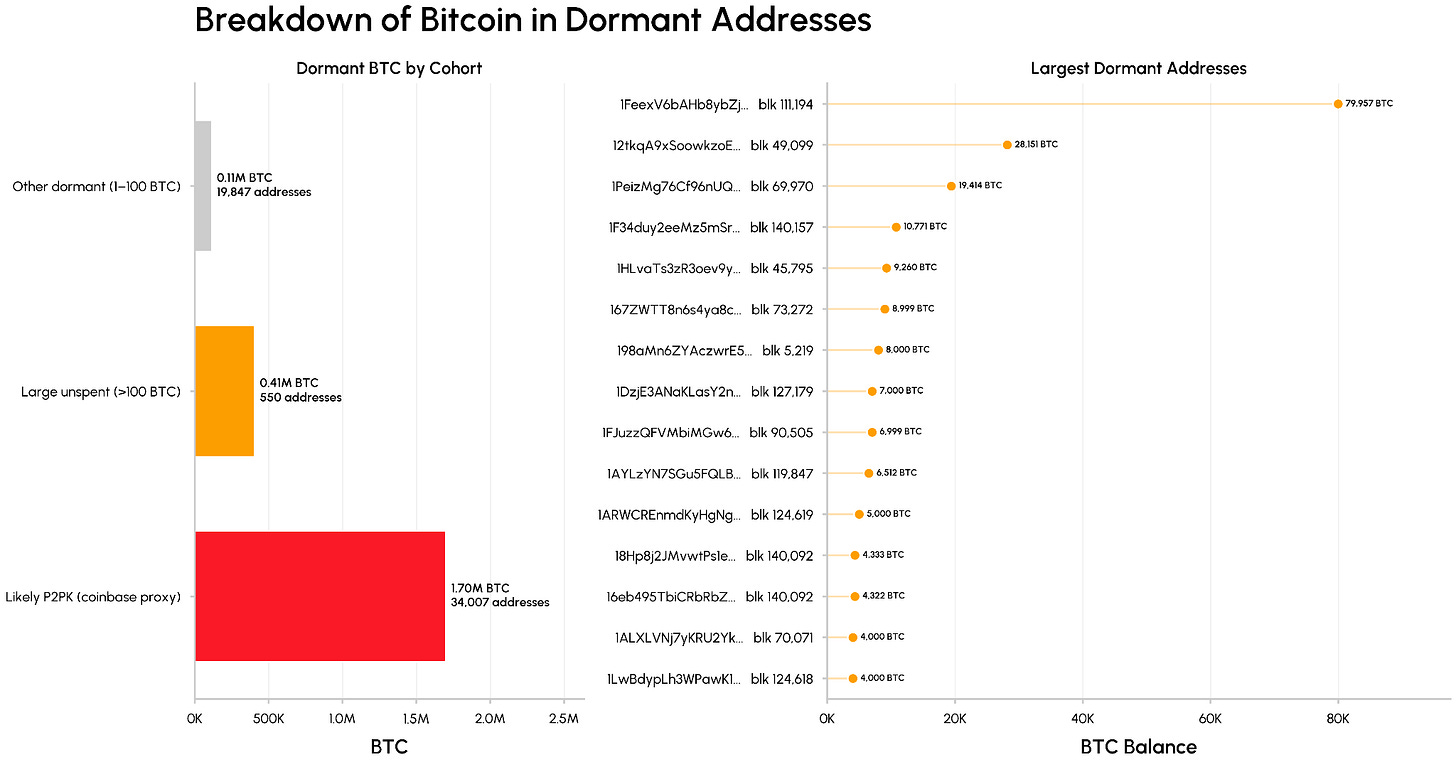
The risk across this pool of dormant coins is not uniform. As seen below, the bulk sits in P2PK coinbase outputs (~1.7M BTC across ~34K addresses), which are the most exposed from a quantum perspective. Other dormant holdings are more distributed, with 0.41M BTC spread over approximately 550 large addresses (containing >100 BTC) and another 0.11M BTC held in nearly 20,000 smaller accounts.
This splits the quantum risk between Satoshi-era P2PK outputs, most vulnerable but spread across many small addresses, and a smaller number of high-value wallets with exposed keys from reuse, such as exchange cold storage wallets, which are more attractive individual targets but can participate more actively in migration.
How does Quantum Risk Differ Across Blockchains?
Quantum risk also varies by network based on address structures, signatures schemes and governance. As we saw, Bitcoin’s main exposure sits at the wallet and UTXO layer, where legacy address types leave a pool of coins whose public keys are exposed, while its proof‑of‑work (PoW) mining and hash functions remain largely safe.
By contrast, blockchains like Ethereum and Solana use account-based models. Under this model, externally owned accounts (EOAs) hold balances behind public keys as soon as those accounts send a transaction, putting a larger share of value at risk than Bitcoin's UTXO model, where many coins remain behind hashes and address reuse is less common. Additionally, proof-of-stake (PoS) chains like Ethereum and Solana have further exposure through the elliptic-curve signatures that validators use to secure the network.
This makes governance and the ability to reach consensus around mitigation, another differentiator for how quickly networks with different properties and levels of decentralization can adopt post-quantum upgrades.
Post-Quantum Proposals and Migration Paths
Bitcoin
Protecting Bitcoin from quantum revolves around enabling post-quantum signatures and migrating coins into these secure address types. This includes the “dormant” supply that cannot migrate easily, cutting at the heart of the Bitcoin governance trade-offs. Proposals being discussed include:
- BIP-360 proposes a new Pay‑to‑Merkle‑Root (P2MR) output type that removes key‑path spends so scripts can keep public keys off‑chain until use, reducing long‑range quantum exposure.
- BIP-361, introduced by a group of researchers including Jameson Lopp proposes a phased sunset of vulnerable signature types over a multi-year timeline. This would first prohibit new deposits to vulnerable address types, and ultimately freeze unmigrated coins including Satoshi’s as a defensive measure against future quantum adversaries.
- To address concerns around freezing dormant coins (the “Satoshi Problem”) Paradigm proposed PACTs (Provable Address-Control Timestamps) which let holders privately create timestamped proofs of address control today without moving coins, so a future quantum‑sunset upgrade could later unlock coins that would otherwise be frozen.
Ethereum and Solana
Ethereum and Solana are taking different but similarly proactive paths. Ethereum has formed a dedicated post-quantum research team, published a roadmap centered on account abstraction and introducing new signature schemes to let validators and users gradually adopt hash-based or lattice-based signatures.
Solana’s Anza and Firedancer validator client teams have independently converged on Falcon, a NIST standardized lattice-based signature scheme, and outlined a three-step plan that would first enable PQ-safe keys, then incentivize gradual rotation, and finally complete migration if quantum risk materializes.
Conclusion
Quantum computing’s threat to blockchain cryptography remains uncertain in timing but increasingly concrete in scope. While no machine today can break elliptic-curve signatures at scale, recent progress has moved the conversation from distant theory to active planning, with the community now building migration paths, testing new signature schemes, and debating how to protect value. For investors and network participants, quantum risk remains a long-dated tail event, not an immediate crisis, but serious enough to warrant preparation and coordination.
Disclaimer: The information herein is provided for informational purposes only. Talos Trading, LLC and its affiliates (“Talos”) does not give any representations or warranties in relation to the accuracy, validity, or completeness of the information of this material, including without limitation the factual information obtained from publicly available sources considered by Talos to be reliable at the time. Talos accepts no liability for any consequences of using the information contained in this material. Any opinions or estimates expressed herein reflect a judgment made by the author(s) as of the date of publication and are subject to change without notice. Neither this material nor any copy thereof may be taken, reproduced, or redistributed, directly or indirectly, without Talos’s prior written permission. Any views or opinions expressed are those of the authors and do not necessarily reflect the views of Talos. This communication does not constitute an offer to buy or sell, or a promotion or recommendation of, any digital asset, security, derivative, commodity, financial instrument, or product or trading strategy. This document and information are not intended to constitute investment advice or a recommendation to make (or refrain from making) any kind of investment decision and may not be relied on as such.
Subscribe
If you’d like to get State of the Network in your inbox, please subscribe below.
Latest insights and research
Request a demo
Find out how Talos can simplify the way you interact with the digital asset markets.






.jpg)